- Features > Sso Authentication
SSO Authentication
Authenticate all CPQ users through your existing identity provider. Mercura supports SAML 2.0 and OIDC — connecting to Okta, Azure AD, Google Workspace, and any enterprise IdP for centralised access control.
SAML 2.0 + OIDC
Identity protocol support
Any IdP
Okta, Azure AD, Google, and more
Zero
Separate CPQ credentials to manage
The Challenge
CPQ Users Are Managing Separate Credentials Outside Your Identity System
Enterprise organisations manage user identity centrally — through Microsoft Azure AD, Okta, Google Workspace, or another Identity Provider (IdP). When CPQ does not support SSO, CPQ users must maintain a separate set of credentials that exist outside the central identity system, creating a security gap and an administrative overhead.
Separate credentials mean separate offboarding risk. When an employee leaves the organisation, deprovisioning their access requires an explicit action in the CPQ system in addition to the central IdP. If this step is missed — as it often is when offboarding is handled under time pressure — the departed employee retains CPQ access long after their IdP account has been disabled.
Password management outside the central IdP also bypasses the organisation's security policies — multi-factor authentication requirements, password complexity rules, session timeout policies. CPQ users on separate credentials may operate without the security controls that apply to every other enterprise application.
For organisations subject to ISO 27001, SOC 2, or similar security frameworks, CPQ access outside the central identity system is a finding. Auditors expect every enterprise application to be governed through the same identity infrastructure — and CPQ is no exception.
How It Works
How SSO Authentication Works in Mercura
Mercura integrates with your organisation's Identity Provider via SAML 2.0 or OpenID Connect (OIDC). Once configured, users access Mercura through your standard SSO flow — clicking the Mercura tile in your IdP portal or navigating to the Mercura URL, which redirects to your IdP for authentication. No Mercura-specific password is required or created. MFA, session policies, and access controls are enforced by the IdP, ensuring CPQ access complies with the same security policies as every other enterprise application. User provisioning can be automated via SCIM — new users are created in Mercura when added to the relevant group in the IdP, and deprovisioned automatically when removed. Mercura roles can be mapped from IdP group membership, eliminating the need to manage role assignments within Mercura separately.
What's Included
Key Capabilities
- SAML 2.0 and OIDC support — compatible with all major enterprise IdPs
- Okta, Microsoft Azure AD, Google Workspace, OneLogin, PingIdentity, and custom IdP support
- IdP-initiated and SP-initiated SSO login flows
- SCIM-based automated user provisioning and deprovisioning
- IdP group-to-Mercura role mapping for automatic permission assignment
- MFA and session policies enforced by the IdP — no CPQ-specific policy configuration needed
- Just-in-time (JIT) user provisioning for first-time SSO login
- Audit log captures all SSO authentication events with IdP identity attribution
The Difference
Before and After SSO Authentication
- CPQ users maintain separate credentials outside the central identity system
- Departed employees retain CPQ access if offboarding step is missed
- MFA and password policies not enforced in CPQ — security gap
- Role assignment managed manually in CPQ — separate from IdP group management
- SSO compliance findings in security audits — CPQ excluded from identity governance
- All CPQ access governed through existing IdP — no separate credentials
- CPQ access revoked automatically when IdP account is disabled
- MFA and session policies from IdP apply to CPQ — security posture consistent
- Mercura roles assigned from IdP groups — access governance centralised
- CPQ fully within identity governance scope — audit findings resolved
Real-World Application
Example Use Case: European Manufacturer Under ISO 27001
A European manufacturing group undergoing ISO 27001 certification received a pre-audit finding that their CPQ system was not integrated with their Okta identity platform. Sales reps were authenticating to Mercura with local credentials that were not subject to the organisation's MFA policy, and the IT team had no systematic process to revoke CPQ access during offboarding. The finding required remediation before certification could proceed. After configuring Mercura's Okta SAML integration and enabling SCIM provisioning, all CPQ authentication moved through Okta. Existing local credentials were disabled. MFA was enforced automatically through Okta's policy. The offboarding process was updated to require only IdP group removal — Mercura access was revoked automatically. The ISO 27001 audit was completed without further identity-related findings.
Quote turnaround dropped from 3 days to under 4 hours.
Business Impact
Why SSO Authentication Matters
SSO integration brings CPQ access under the same governance framework as every other enterprise application — closing the security gap that separate credentials create, ensuring that security policies apply consistently, and simplifying access management for IT teams. For organisations operating under security frameworks or facing external audits, SSO is not optional — it is a baseline requirement. Mercura's SSO implementation is designed to satisfy that requirement without friction, connecting to any SAML or OIDC-compliant identity provider in a standard configuration that IT teams can complete without professional services involvement.
Connect Mercura to Your Identity Provider
Book a demo to see how Mercura's SSO integration brings CPQ access under your central identity governance framework.
Let’s build together.
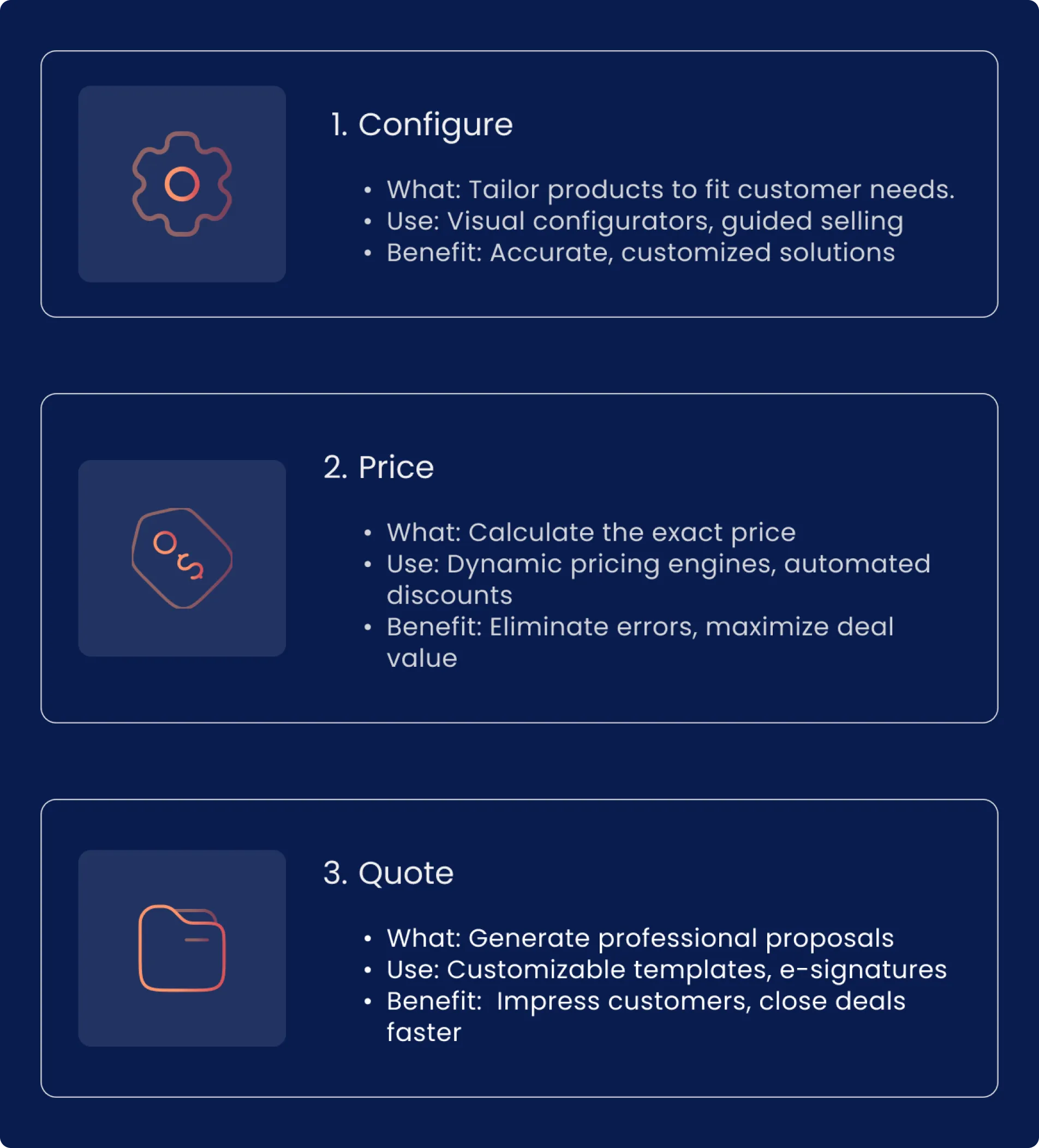
We empower manufacturers to master product modeling, streamline quoting process, reduce errors, and ultimately deliver the tailored solutions that customers demand.